| 1 |
 |
Vehicular Communication Basics |
13 years, 2 months |
SecurityTube_Bot |
basics |
5627 |
None |
| 2 |
 |
Vehicular Communication Basics (2) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7248 |
None |
| 3 |
 |
Vehicular Communication Basics (3) |
13 years, 2 months |
SecurityTube_Bot |
basics |
4978 |
None |
| 4 |
 |
Rc4 Basics Presentation |
13 years, 2 months |
SecurityTube_Bot |
basics |
12426 |
1 |
| 5 |
 |
Rc4 Simulation Using C |
13 years, 2 months |
SecurityTube_Bot |
basics |
7712 |
1 |
| 6 |
 |
Rc4 File Encrypt Decrypt Program |
13 years, 2 months |
SecurityTube_Bot |
basics |
15287 |
2 |
| 7 |
 |
Internet Worm Basics Presentation |
13 years, 2 months |
SecurityTube_Bot |
basics |
9074 |
1 |
| 8 |
 |
Internet Worm Basics Presentation (2) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8529 |
None |
| 9 |
 |
Internet Worm Ip Scanning Programming |
13 years, 2 months |
SecurityTube_Bot |
basics |
7801 |
3 |
| 10 |
 |
Internet Worm Basics Presentation |
13 years, 2 months |
SecurityTube_Bot |
basics |
6418 |
None |
| 11 |
 |
Internet Worm Ip Scanning Programming (2) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6058 |
None |
| 12 |
 |
Rc4 Basics Presentation (2) |
13 years, 2 months |
SecurityTube_Bot |
basics |
9500 |
None |
| 13 |
 |
Wireless Frames Format And Types |
13 years, 2 months |
SecurityTube_Bot |
basics |
8294 |
None |
| 14 |
 |
Wifi Mac Header (Part 1) |
13 years, 2 months |
SecurityTube_Bot |
basics |
10655 |
None |
| 15 |
 |
Wifi Mac Header (Part 2) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7128 |
None |
| 16 |
 |
Connecting Wireless Station To Ap |
13 years, 2 months |
SecurityTube_Bot |
basics |
5830 |
None |
| 17 |
 |
Wifi State Machine (Part 1) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7754 |
None |
| 18 |
 |
Wifi State Machine (Part 2) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6604 |
None |
| 19 |
 |
Wifi State Machine (Part 3) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5948 |
None |
| 20 |
 |
Virtual Carrier Sensing (Nav) Mechanism |
13 years, 2 months |
SecurityTube_Bot |
basics |
14011 |
1 |
| 21 |
 |
How Spammers Abuse Whois And Smtp Part 1 |
13 years, 2 months |
SecurityTube_Bot |
basics |
5990 |
None |
| 22 |
 |
How Spammers Abuse Whois And Smtp Part 2 |
13 years, 2 months |
SecurityTube_Bot |
basics |
5376 |
None |
| 23 |
 |
How Spammers Abuse Whois And Smtp Part 3 |
13 years, 2 months |
SecurityTube_Bot |
basics |
5459 |
None |
| 24 |
 |
Access Control (Csma Cd) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8344 |
1 |
| 25 |
 |
Csma Ca |
13 years, 2 months |
SecurityTube_Bot |
basics |
14819 |
None |
| 26 |
 |
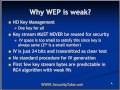
Wep Tutorial 1 |
13 years, 2 months |
SecurityTube_Bot |
basics |
8824 |
1 |
| 27 |
 |
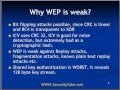
Wep Tutorial 2 |
13 years, 2 months |
SecurityTube_Bot |
basics |
6272 |
None |
| 28 |
 |
Wep Tutorial 3 |
13 years, 2 months |
SecurityTube_Bot |
basics |
7971 |
None |
| 29 |
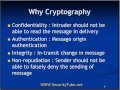 |
Cryptography (Introduction) |
13 years, 2 months |
SecurityTube_Bot |
basics |
14353 |
None |
| 30 |
 |
Ieee 802.11w And Cisco Mfp I |
13 years, 2 months |
SecurityTube_Bot |
basics |
8070 |
None |
| 31 |
 |
Ieee 802.11w And Cisco Mfp Ii |
13 years, 2 months |
SecurityTube_Bot |
basics |
6980 |
None |
| 32 |
 |
Cryptoanalysis (Types Of Attacks On Cryptography) |
13 years, 2 months |
SecurityTube_Bot |
basics |
28468 |
None |
| 33 |
 |
Symmetric Key Cryptography |
13 years, 2 months |
SecurityTube_Bot |
basics |
12145 |
6 |
| 34 |
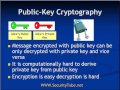 |
Public Key Cryptography |
13 years, 2 months |
SecurityTube_Bot |
basics |
16629 |
None |
| 35 |
 |
Installing Backtrack 3 On Vmware Workstation |
13 years, 2 months |
SecurityTube_Bot |
basics |
29640 |
1 |
| 36 |
 |
Ipv6 101 Whats New In Ipv6 |
13 years, 2 months |
SecurityTube_Bot |
basics |
9328 |
None |
| 37 |
 |
Ipv6 Address Space |
13 years, 2 months |
SecurityTube_Bot |
basics |
8780 |
None |
| 38 |
 |
Ipv6 Header Structure |
13 years, 2 months |
SecurityTube_Bot |
basics |
10852 |
None |
| 39 |
 |
How To Assign Ipv6 Address |
13 years, 2 months |
SecurityTube_Bot |
basics |
19049 |
None |
| 40 |
 |
Eui 64 A Building Block For Auto Configuration In Ipv6 |
13 years, 2 months |
SecurityTube_Bot |
basics |
7912 |
None |
| 41 |
 |
Backtrack 3 Hard Drive Installation (Infinity Exists) |
13 years, 2 months |
SecurityTube_Bot |
basics |
18906 |
1 |
| 42 |
 |
Ten Cool Things You Did Not Know About Your Hard Drive |
13 years, 2 months |
SecurityTube_Bot |
basics |
44959 |
1 |
| 43 |
 |
Dns Spoofing With Virtual Hosts |
13 years, 2 months |
SecurityTube_Bot |
basics |
15959 |
None |
| 44 |
 |
Defeating Ssl Using Sslstrip (Marlinspike Blackhat) |
13 years, 2 months |
SecurityTube_Bot |
basics |
83199 |
3 |
| 45 |
 |
Attacking Intel Trusted Execution Technology (Wojtczuk Rukowska) |
13 years, 2 months |
SecurityTube_Bot |
basics |
9290 |
None |
| 46 |
 |
Active Https Cookie Hijacking (Mike Defcon 16) |
13 years, 2 months |
SecurityTube_Bot |
basics |
12581 |
None |
| 47 |
 |
Demonstration Of Hardware Trojans (Defcon 16) |
13 years, 2 months |
SecurityTube_Bot |
basics |
10509 |
None |
| 48 |
 |
Scanning The Internet With Nmap (Defcon 16) |
13 years, 2 months |
SecurityTube_Bot |
basics |
20577 |
None |
| 49 |
 |
Anti Forensics Techniques For Osx (Vincenzo Blackhat Dc) |
13 years, 2 months |
SecurityTube_Bot |
basics |
12778 |
None |
| 50 |
 |
Hijacking The Internet Using A Bgp Mitm Attack (Defcon 16) |
13 years, 2 months |
SecurityTube_Bot |
basics |
21349 |
None |
| 51 |
 |
Making Money On The Web The Blackhat Way |
13 years, 2 months |
SecurityTube_Bot |
basics |
11180 |
2 |
| 52 |
 |
Cross Site Request Forgery (Csrf) Tutorial |
13 years, 2 months |
SecurityTube_Bot |
basics |
31122 |
None |
| 53 |
 |
Cross Site Scripting (Xss) Primer |
13 years, 2 months |
SecurityTube_Bot |
basics |
26335 |
2 |
| 54 |
 |
Openx Vulnerability Scan With Acunetix Web Vulnerability Scanner |
13 years, 2 months |
SecurityTube_Bot |
basics |
8588 |
None |
| 55 |
 |
Auditing Flex Amf3 And Blazeds Based Rias (Blackhat 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7431 |
None |
| 56 |
 |
Hacking Flash Applications For Fun And Profit (Blackhat) |
13 years, 2 months |
SecurityTube_Bot |
basics |
32284 |
None |
| 57 |
 |
Understanding The Tcp 3 Way Handshake |
13 years, 2 months |
SecurityTube_Bot |
basics |
13511 |
None |
| 58 |
 |
Firewalls (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6576 |
None |
| 59 |
 |
Vulnerability Scanning (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6305 |
None |
| 60 |
 |
Snort Overview (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8932 |
None |
| 61 |
 |
Computer Hardware Basics (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6605 |
None |
| 62 |
 |
How To Covertly Monitor Encrypted Wifi Networks |
13 years, 2 months |
SecurityTube_Bot |
basics |
16029 |
None |
| 63 |
 |
Physical Security (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5619 |
None |
| 64 |
 |
Enumeration (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5892 |
None |
| 65 |
 |
A Brief Tour Of Ubuntu 9 (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6535 |
None |
| 66 |
 |
Trojans (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6386 |
None |
| 67 |
 |
Sql Injection Primer (Imperva) |
13 years, 2 months |
SecurityTube_Bot |
basics |
19337 |
None |
| 68 |
 |
Denial Of Service (Dos) Attack (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8223 |
None |
| 69 |
 |
Sql Injection Attack (Corky's Security Series) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6846 |
None |
| 70 |
 |
Attacking Internet Backbone Technologies (Blackhat 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8446 |
None |
| 71 |
 |
Sap Penetration Testing (Blackhat 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
15926 |
None |
| 72 |
 |
Satellite Hacking For Fun And Profit (Blackhat 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
35583 |
None |
| 73 |
 |
Hacking Mac Os X And Iphone Payloads |
13 years, 2 months |
SecurityTube_Bot |
basics |
12547 |
1 |
| 74 |
 |
Sql Injection Worms For Fun And Profit |
13 years, 2 months |
SecurityTube_Bot |
basics |
9936 |
None |
| 75 |
 |
Cisco Ios Shellcode Hacking |
13 years, 2 months |
SecurityTube_Bot |
basics |
13049 |
None |
| 76 |
 |
Beating Phishers At Their Own Game |
13 years, 2 months |
SecurityTube_Bot |
basics |
12351 |
None |
| 77 |
 |
Exploiting The Nic Chipset |
13 years, 2 months |
SecurityTube_Bot |
basics |
9296 |
None |
| 78 |
 |
System Management Mode Rootkit |
13 years, 2 months |
SecurityTube_Bot |
basics |
8486 |
None |
| 79 |
 |
Vulnerability Management In An Application Security World (Owasp) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7531 |
None |
| 80 |
 |
Proactive Lifecycle Security Management (Owasp) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5688 |
None |
| 81 |
 |
Hacker Commerce Episode 1 |
13 years, 2 months |
SecurityTube_Bot |
basics |
7087 |
None |
| 82 |
 |
Http Parameter Pollution (Hpp) Attack |
13 years, 2 months |
SecurityTube_Bot |
basics |
19282 |
None |
| 83 |
 |
Client Side Penetration Testing (Notacon) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6452 |
None |
| 84 |
 |
How I Learned Reverse Engineering With Storm (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7178 |
None |
| 85 |
 |
Methods For Analyzing Malicious Office Documents (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6126 |
None |
| 86 |
 |
Building Plugins For Ida Pro (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8305 |
None |
| 87 |
 |
Windows Privilege Escalation Through Lpc And Alpc Interfaces (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6919 |
None |
| 88 |
 |
Netware Kernel Stack Overflow Exploitation (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7004 |
None |
| 89 |
 |
Under The Ihood (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5659 |
None |
| 90 |
 |
Helikaon Linux Debugger (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7231 |
None |
| 91 |
 |
Creating Code Obfuscation Virtual Machines (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8550 |
None |
| 92 |
 |
The Deobfuscator (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7165 |
None |
| 93 |
 |
Polymorphic Virus Analysis (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7495 |
None |
| 94 |
 |
Hacking The Asus Wl520gu Wireless Router (Notacon) |
13 years, 2 months |
SecurityTube_Bot |
basics |
11007 |
None |
| 95 |
 |
Hacking Culture (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7203 |
None |
| 96 |
 |
Bypassing Security Protections By Backdooring Libc |
13 years, 2 months |
SecurityTube_Bot |
basics |
6771 |
None |
| 97 |
 |
Blackbox Reversing Of Xss Filters (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6853 |
None |
| 98 |
 |
Damn Vulnerable Web App Installation |
13 years, 2 months |
SecurityTube_Bot |
basics |
12684 |
None |
| 99 |
 |
Reverse Engineering Dynamic Languages (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6019 |
None |
| 100 |
 |
Social Engineering For The Socially Inept (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7741 |
None |
| 101 |
 |
Iis Webdav Vulnerability In Action |
13 years, 2 months |
SecurityTube_Bot |
basics |
14952 |
None |
| 102 |
 |
Fuzzing In Action Using Hzzp |
13 years, 2 months |
SecurityTube_Bot |
basics |
8182 |
None |
| 103 |
 |
Metasploit Visual Basic Payloads In Action |
13 years, 2 months |
SecurityTube_Bot |
basics |
8981 |
1 |
| 104 |
 |
L0phtcrack 6 Demo |
13 years, 2 months |
SecurityTube_Bot |
basics |
10317 |
None |
| 105 |
 |
Owasp Testing Guide V3 And Secure Software Development |
13 years, 2 months |
SecurityTube_Bot |
basics |
8435 |
None |
| 106 |
 |
Reverse Engineering Of Proprietary Protocols, Tools And Techniques |
13 years, 2 months |
SecurityTube_Bot |
basics |
7379 |
None |
| 107 |
 |
Owasp Webscarab Ng |
13 years, 2 months |
SecurityTube_Bot |
basics |
11614 |
None |
| 108 |
 |
Netifera (Java Virtual Machine As Shellcode) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8009 |
None |
| 109 |
 |
Top Ten Web Hacking Techniques Of 2008 (Snowfroc) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7664 |
None |
| 110 |
 |
Automate Or Die (Snowfroc) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5628 |
None |
| 111 |
 |
Adobe Flex, Amf 3 And Blazeds An Assessment (Snowfroc) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7003 |
None |
| 112 |
 |
Building An Effective Application Security Program (Snowfroc) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5605 |
None |
| 113 |
 |
Spear Phishing And Application Hacks (Snowfroc) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6041 |
None |
| 114 |
 |
Sql Injection But Not Only And 1 Eq 1 (Snowfroc) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7157 |
None |
| 115 |
 |
Security Policy Management (Best Practices For Web Services And Application Security) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6431 |
None |
| 116 |
 |
Vulnerability Management In An Application Security World (Snowfroc) |
13 years, 2 months |
SecurityTube_Bot |
basics |
4988 |
None |
| 117 |
 |
Reverse Engineering Over Acrobat Reader Using Immunity Debugger (Recon) |
13 years, 2 months |
SecurityTube_Bot |
basics |
17039 |
None |
| 118 |
 |
Two Very Small Reverse Engineering Tools (Recon) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6956 |
None |
| 119 |
 |
How Secure Is Your Forum Login |
13 years, 2 months |
SecurityTube_Bot |
basics |
8120 |
2 |
| 120 |
 |
Is Xss Solveable (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5366 |
None |
| 121 |
 |
Advanced Sql Injection (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
10889 |
None |
| 122 |
 |
Hacking With Gnuradio (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
10077 |
None |
| 123 |
 |
Deploying Dnssec (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7039 |
None |
| 124 |
 |
Policy, The Biscuit Game Of Infosec (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5142 |
None |
| 125 |
 |
Lockpicking Forensics (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6842 |
None |
| 126 |
 |
Diplomatic Security Consulting (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5708 |
None |
| 127 |
 |
Why Your Mother Will Never Care About Linux (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6217 |
None |
| 128 |
 |
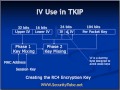
Tkip Introduction (Part I) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6067 |
None |
| 129 |
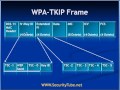 |
Tkip Introduction (Part Ii) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7199 |
None |
| 130 |
 |
Can You Build A Wifi Jammer |
13 years, 2 months |
SecurityTube_Bot |
basics |
53123 |
2 |
| 131 |
 |
Packing And The Friendly Skies (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5611 |
None |
| 132 |
 |
Twatfs, Surly Abuse Of Social Networking Bandwidth (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5889 |
None |
| 133 |
 |
Incident Response 101 (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5805 |
None |
| 134 |
 |
Computation And Modeling (Layerone 2009) |
13 years, 2 months |
SecurityTube_Bot |
basics |
5521 |
None |
| 135 |
 |
Introduction To Ethical Hacking, Penetration Testing And Countermeasures |
13 years, 2 months |
SecurityTube_Bot |
basics |
19097 |
None |
| 136 |
 |
Applied Reverse Engineering On Os X (Recon 2008) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7331 |
None |
| 137 |
 |
Tkip Primer Mic (Message Integrity Code) |
13 years, 2 months |
SecurityTube_Bot |
basics |
9286 |
None |
| 138 |
 |
Tkip Primer Tkip Sequence Counter |
13 years, 2 months |
SecurityTube_Bot |
basics |
6474 |
None |
| 139 |
 |
The Ultimate Commodore 64 Talk (25c3) |
13 years, 2 months |
SecurityTube_Bot |
basics |
11010 |
None |
| 140 |
 |
Tcp Denial Of Service Vulnerabilities (25c3) |
13 years, 2 months |
SecurityTube_Bot |
basics |
7115 |
None |
| 141 |
 |
Full Disk Encryption Crash Course (25c3) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8339 |
None |
| 142 |
 |
Chip Reverse Engineering (25c3) |
13 years, 2 months |
SecurityTube_Bot |
basics |
9751 |
None |
| 143 |
 |
Hacking The Iphone (25c3) |
13 years, 2 months |
SecurityTube_Bot |
basics |
8287 |
None |
| 144 |
 |
Tkip Primer (Part I) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6280 |
None |
| 145 |
 |
Tkip Primer (Part Ii) |
13 years, 2 months |
SecurityTube_Bot |
basics |
6447 |
None |
| 146 |
 |
Iphone Forensics (Live Recovery Over Usb) |
13 years, 2 months |
SecurityTube_Bot |
basics |
15728 |
None |
| 147 |
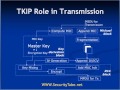 |
Tkip Primer Encapsulation |
13 years, 2 months |
SecurityTube_Bot |
basics |
6745 |
None |
| 148 |
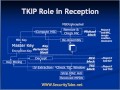 |
Tkip Primer Decapsulation |
13 years, 2 months |
SecurityTube_Bot |
basics |
5674 |
None |
| 149 |
 |
Dns Cache Poisoning Attack |
13 years, 2 months |
SecurityTube_Bot |
basics |
14979 |
None |
| 150 |
 |
W3af (A Framework To Own The Web) |
13 years, 2 months |
SecurityTube_Bot |
basics |
13321 |
None |